Shadow AI Playbook for IT Leaders: From Detection to a Secure Enterprise Sandbox
Imagine a scenario where a key employee, in a rush to meet a deadline, pastes the details of a strategic plan into a public chatbot to get a quick summary. With that single action, trade secrets can slip out of your control and may end up in an uncontrolled, third-party environment. This is the reality of Shadow AI, where security depends not on the firewall, but on the split-second decision of a hurried colleague.
This playbook helps you detect risks, and we show you how to build an environment where innovation and security coexist.
How do I know if Shadow AI exists in my organization?
Shadow AI tends to spread quietly, but there are telltale indicators. Watch for network traffic and workflows where document analysis or report generation suddenly speeds up without approved software implementations. Surges in outbound traffic directed toward public platforms are often a signal that people are using unsanctioned AI tools and bypassing internal policies.
The most common signs are the following:
- Surges in outbound traffic toward public generative AI domains during working hours.
- Suddenly, complex contract summaries or proposal comparisons appear without new official tools.
- New browser extensions appear that automatically summarize or highlight content, bypassing internal approval.
- More "send me the doc and I'll tell you" requests and fewer "where can I find it" searches, pointing to document processing in external tools.
Which data is most at risk, and how do we prevent data leakage?
The source of data leakage is often the well-meaning employee seeking efficiency, and certain information should never end up in public, out-of-policy AI services due to EU AI Act or GDPR compliance. The protection of critical data assets and sensitive data is a fundamental expectation for compliance, and security does not end with blocking.
The most important items on the restricted data list:
- Strategic financial plans and trade secrets.
- Details of custom software coding.
- Personal customer data.
- Internal contractual clauses and terms.
The basis of prevention is a clear internal AI policy and providing a technological alternative by creating a secure internal AI environment. On the supplier side, this includes conducting thorough due diligence to ensure you know what data management and liability frameworks the service provider undertakes.
What makes AI usage controlled: data loss prevention (DLP) for generative AI, logging, and audit logging?
The basis of transparent operation is traceability, and the lack of control is a serious compliance risk. Reliable operation requires a dedicated AI monitoring system that ensures process transparency and protects confidential information.
The technical pillars of security:
- RBAC-based access management aligned with the hierarchy.
- Continuous logging, and a comprehensive audit log with user-level traceability for compliance reviews.
- Auditable answers with source references and document-level traceability for fact-based decisions.
These functions support compliance controls under NIS2 and the AI Act. If you are curious about how this becomes a true assistant for colleagues, read our article on how faster onboarding correlates with fewer question marks.

Why are on-premisess and data residency critical in business decisions?
The concept of data residency helps ensure confidential information remains within the network perimeter and does not enter an external environment. A flexible architecture allows for choice according to your own rules, supports data sovereignty, and helps meet strict data residency requirements.
The advantages of selectable deployment directions:
- On-premises: The system runs on the company's own hardware, so not a single byte of information leaves your infrastructure, representing the highest security level.
- Private cloud: Operation takes place in a dedicated and isolated cloud infrastructure, combining scalability with the protection of a closed environment.
- Hybrid architecture: The sensitive knowledge base remains local, and computational tasks run in the cloud via an encrypted channel.
Everyday risk is born when a colleague looks for workarounds, and this is where it is decided whether we prohibit or provide an internal path.
When should I not use AI, and how do I build a secure enterprise sandbox?
Never use a tool that does not guarantee data isolation or where the source of answers remains unverifiable. It is also risky if the privacy policy does not reassuringly protect company ownership rights.
Before implementation, it is worth thoroughly weighing strategic aspects, which is why we prepared a summary on what you need to consider before introducing an AI knowledge platform into the organizational environment.
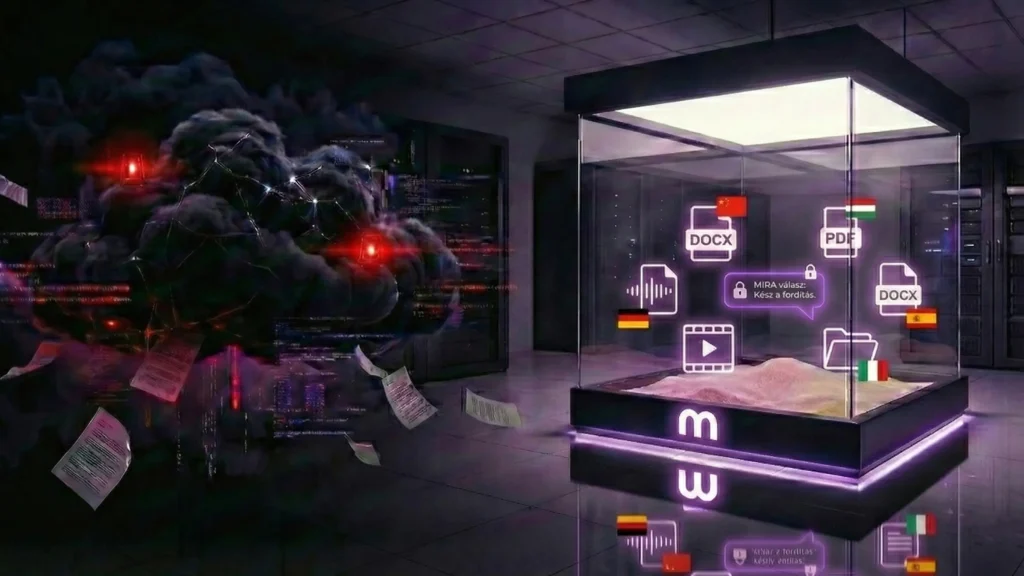
You can effectively reduce reliance on public AI tools by offering a professional, sanctioned alternative like MIRA. This platform is a protected enterprise sandbox that runs on your own server or in a closed cloud, within your approved environment and governance controls.
In addition to maintaining data sovereignty, AI-supported workflows also become secure within this framework. This is particularly critical for tasks performed in multilingual environments, where colleagues are often forced to use external, insecure tools to interpret documents. Through our solution supporting effective collaboration for international teams, sensitive data remains entirely within the internal network, while information processing becomes seamless without anyone needing to resort to risky public platforms.
The system is prepared for Samba-based synchronization, so it is capable of working directly from your own folders, and data management remains in-house throughout. Modern leadership is about secure alternatives, and with these, hidden processes turn into business value.
[banner type="mira" text="Take control and mitigate Shadow AI risks!" button="Request expert consultation!" link="https://encomira.hu/contact"]

